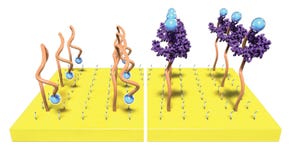
New Technologies
thumbnail
Product Development
Proven Insights for Efficient Medical Device Design & DevelopmentPractical Insights for Medical Device Design & Development
A look at the tools and strategies you need for strong product development.
Sign up for the QMED & MD+DI Daily newsletter.